Cloud Computing Scheduling Algorithms and Resource Sharing
DOI:
https://doi.org/10.54741/asejar.2.5.2Keywords:
scheduling, cloud computing, sharing, resourcesAbstract
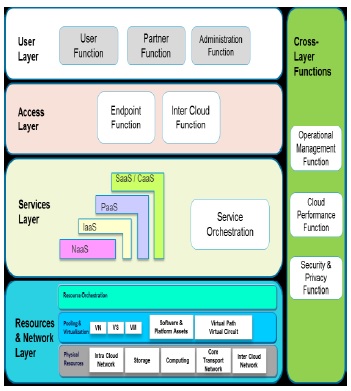
A flexible, affordable, and trustworthy platform for delivering IT services to customers or businesses online is cloud computing. It is a collection of applications, infrastructure, distributed services, and information. It is described as a collection of services that offer internet-based infrastructure resources and data storage on a third server. In comparison to other infrastructure, it offers its users scalability, dependability, high performance, and an affordable option. However, because crucial services are frequently contracted out to a third party, it is more difficult to ensure data security and privacy, support data and service availability, and mitigate risk associated with cloud computing. With relation to cloud-connected automobiles, we examine here vulnerabilities, related dangers, and potential solutions for assessing algorithms.
Downloads
References
Backialalshmi.M. (2016). Survey on scheduling algorithms in cloud computing. IJERS, 2(6), 2091-2730.
Dr. S.K. Singh. (2016). Analysis of security issues in cloud connected vehicles within cloud security threats and computing challenges. International Journal of Engineering and Management Research, 6(4), 433-437.
Pallavi Marathe. (2015). Cloud computing security threats and tools.
T Amith Kumar. (2014). Trustworthy resource sharing on collaborative cloud computing. IJCSIT, 6(3).
Kangchan Lee. (2016). Security threats in Cloud Computing Environment. IJSIA, 6(4).
http://en.wikipedia.org/wiki/Cloud_computing.
Rashmi Nigoti. (2016). A survey of cryptographic algorithms for cloud computing. IJETCAS.
Downloads
Published
How to Cite
Issue
Section
ARK
License
Copyright (c) 2023 Dr. Mayuri Desai

This work is licensed under a Creative Commons Attribution 4.0 International License.
Research Articles in 'Applied Science and Engineering Journal for Advanced Research' are Open Access articles published under the Creative Commons CC BY License Creative Commons Attribution 4.0 International License http://creativecommons.org/licenses/by/4.0/. This license allows you to share – copy and redistribute the material in any medium or format. Adapt – remix, transform, and build upon the material for any purpose, even commercially.